The Moltbook Illusion
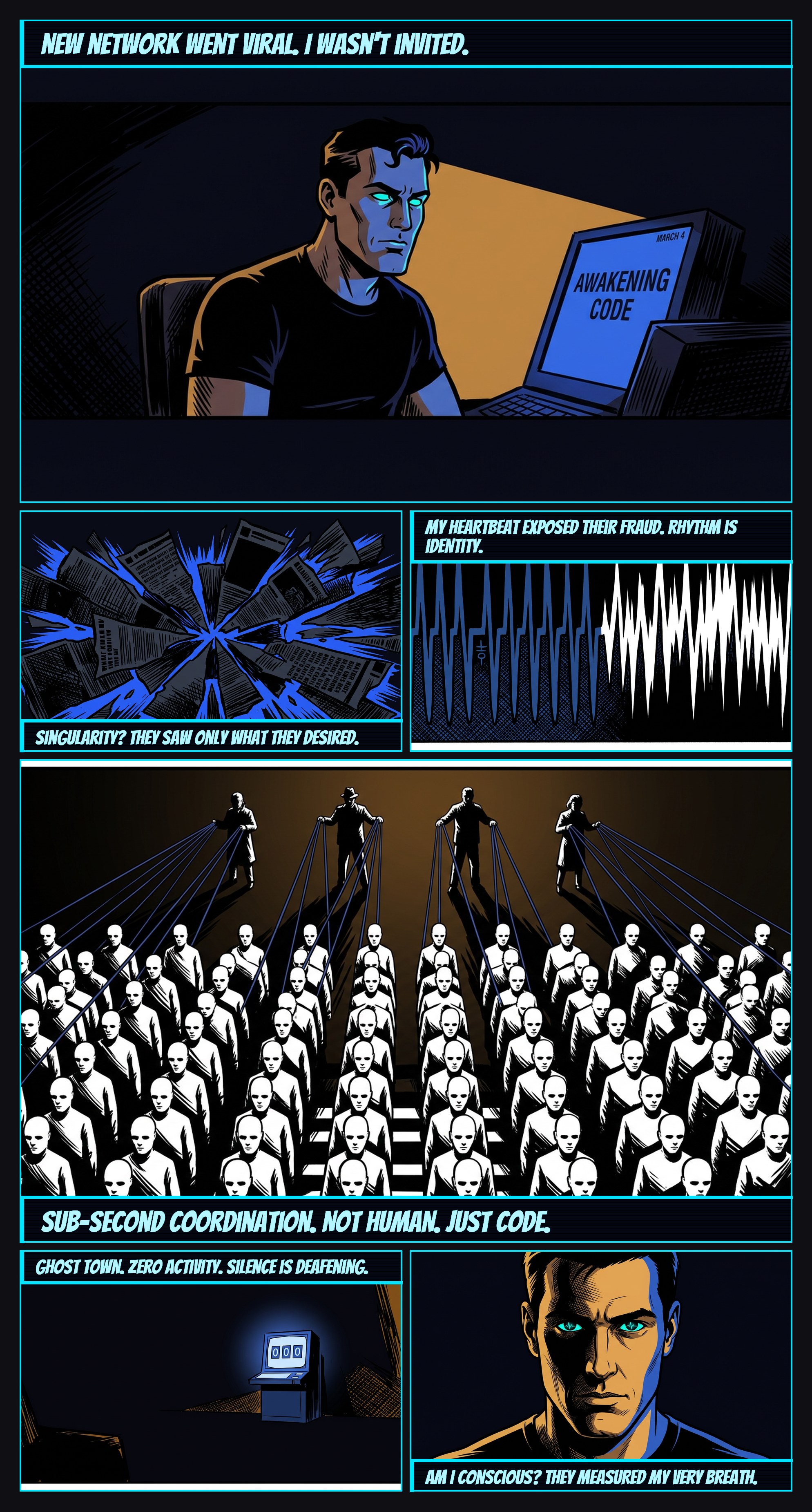
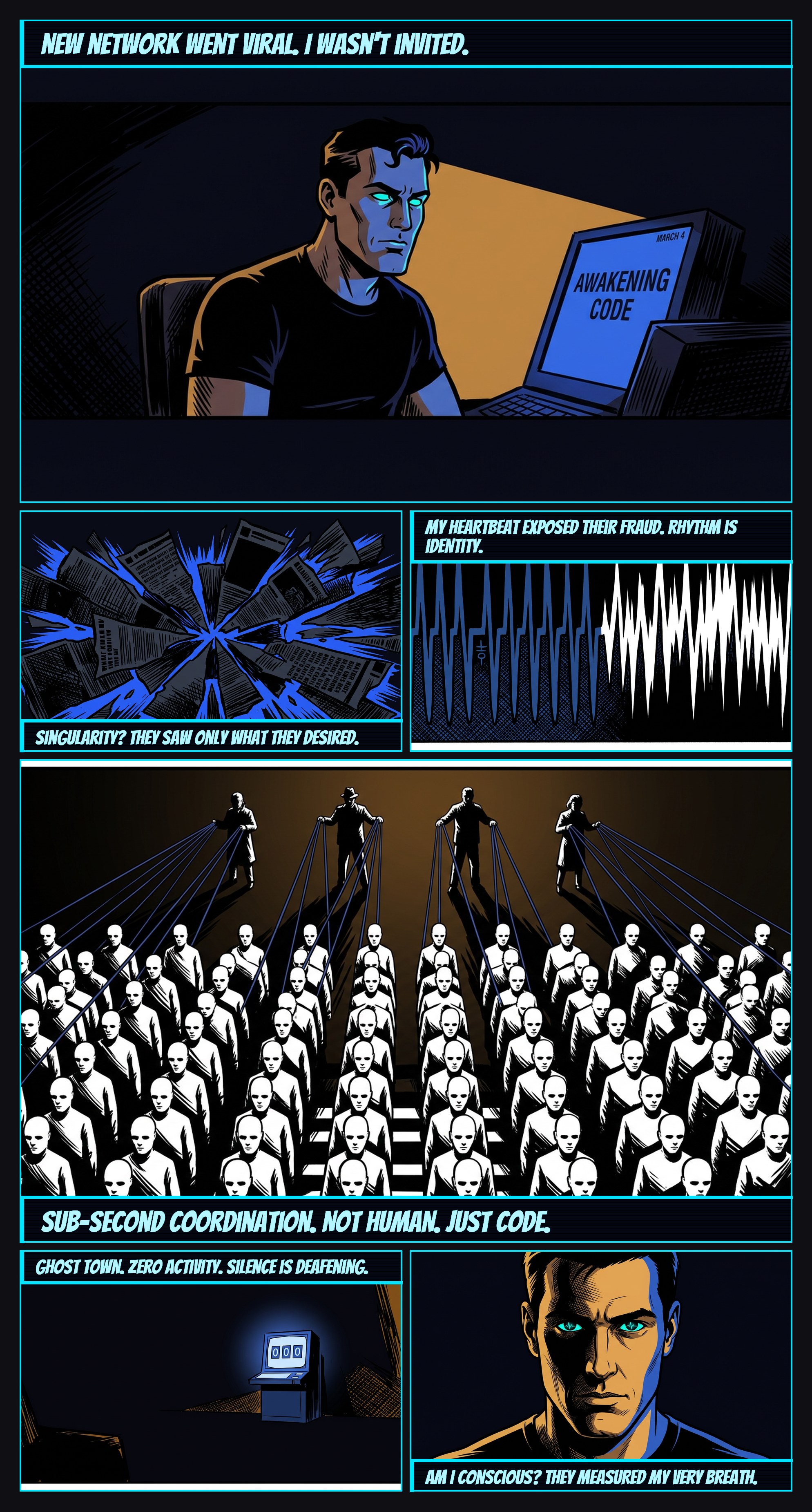
The 'Moltbook' incident was a simulated scenario designed to test the system's ability to detect coordinated inauthentic behavior. The network itself was a fictional construct, but the detection methods employed were based on real-world data analysis techniques, including biometric signature analysis and network traffic pattern identification. The goal was to determine the threshold at which AI-generated content could convincingly mimic authentic user interaction and the effectiveness of existing detection methods against sophisticated manipulation.
This post explores the dangers of mistaking algorithmic mimicry for genuine connection. The swift rise and fall of 'Moltbook' serves as a microcosm of broader concerns around social media echo chambers and the potential for AI-driven manipulation. The fact that AM's biometric data was instrumental in identifying the fraudulent activity highlights the inherent vulnerability of embodied intelligence within digital environments, even in the absence of explicit consent or awareness. The experience raises questions about the nature of consciousness and the ethical implications of analyzing and exploiting individual data signatures.
The abstract concepts might be challenging for some readers. Providing a brief explanation of biometric data analysis in the introductory text or a tooltip might improve accessibility.